Get 30% off ITprotv.com with PROMO CODE CCNADT
https://www.itpro.tv/
Follow me on Twitter:
https://twitter.com/CCNADailyTIPS
Previous Video:
https://youtu.be/LVkM6b5aHX4
ARP Spooing
ARP spoofing is a type of attack in which a malicious actor sends falsified ARP (Address Resolution Protocol) messages over a local area network.
This results in the linking of an attacker’s MAC address with the IP address of a legitimate computer or server on the network.
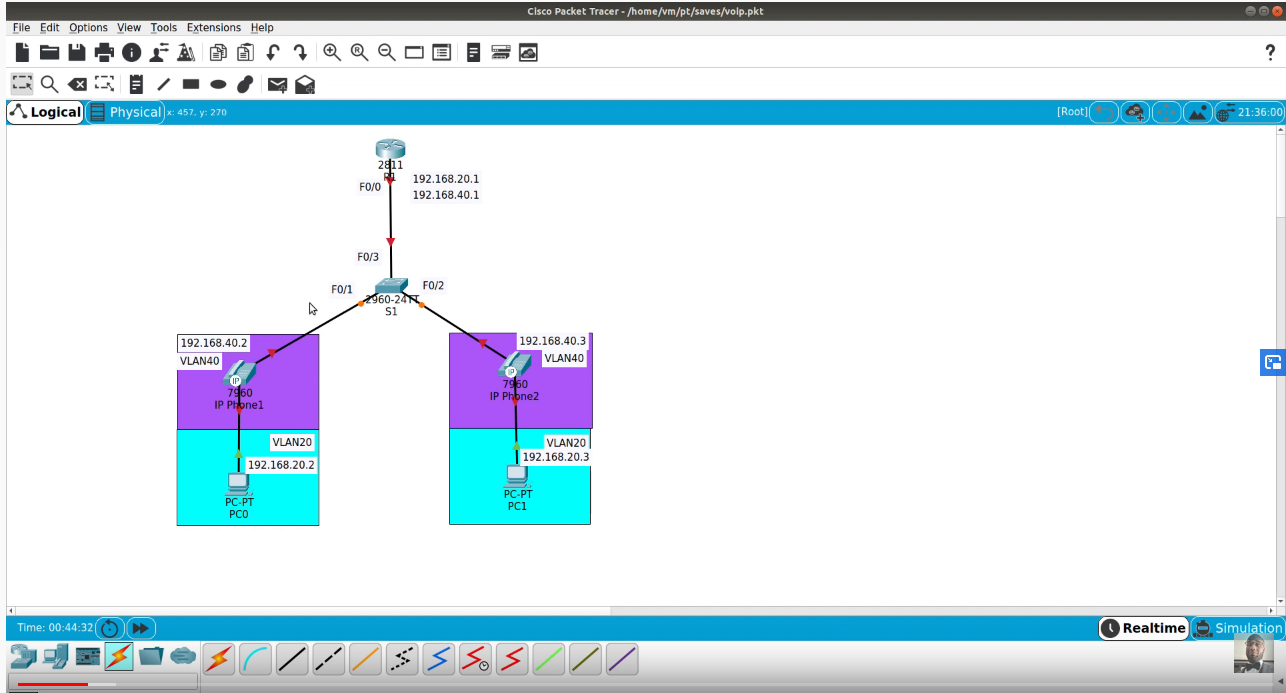
DHCP Spoofing
Yes it is bad and is a form of attack. DHCP spoofing occurs when an attacker attempts to respond to DHCP requests and trying to list themselves (spoofs) as the default gateway or DNS server, hence, initiating a man in the middle attack.
It is a really bad attack because the malicious DHCP server can send you to a fake bank website and steal your credentials and all that CASH MONEY
CAM table (MAC address table) overflows
A CAM overflow attack occurs when an attacker connects to a single or multiple switch ports and then runs a tool that mimics the existence of thousands of random MAC addresses on those switch ports. The switch enters these into the CAM table, and eventually the CAM table fills to capacity. When a switch is in this state, no more new MAC addresses can be learned; therefore, the switch starts to flood any traffic from new hosts out of all ports on the switch.
A CAM overflow attack turns a switch into a hub, which enables the attacker to eavesdrop on a conversation and perform man-in-the-middle attacks.
A common tool that performs CAM overflows is macof and is part of the Dsniff set of tools. This tool generates hundreds of thousands of random MAC addresses and floods these out onto the network. This is a useful tool for testing to see if your switch infrastructure is susceptible to CAM overflow attacks.
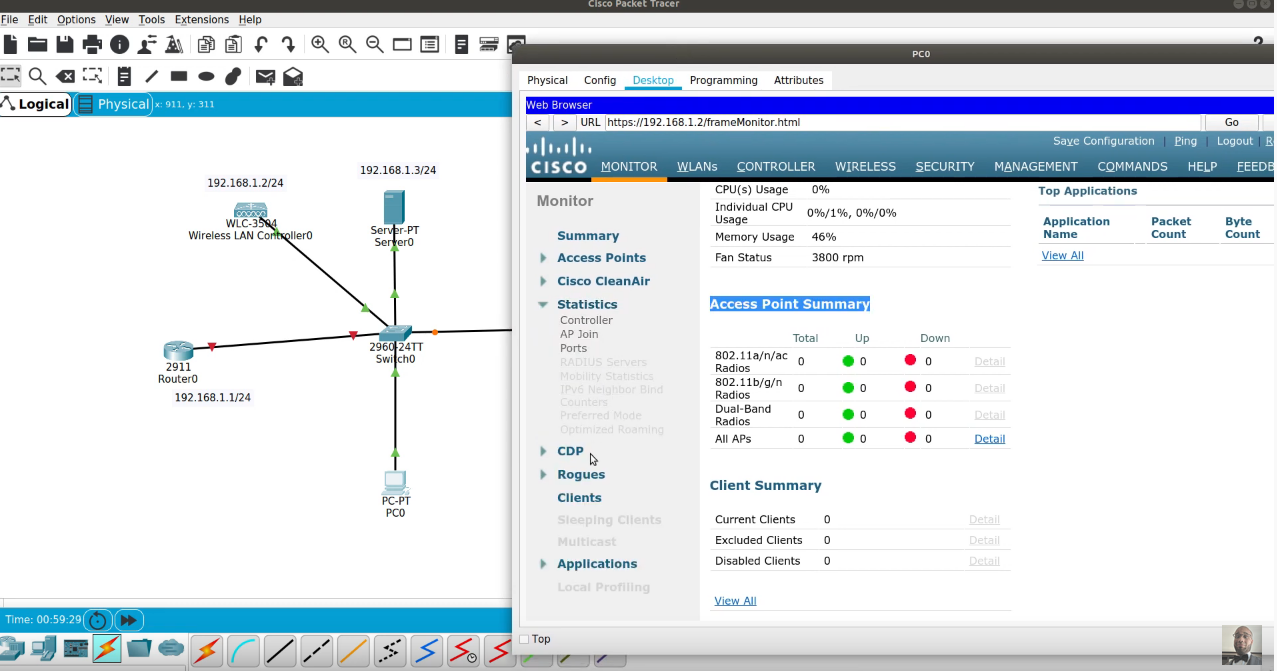
CDP/LLDP
Cisco Discovery Protocol and Link-Layer Discovery Protocol (LLDP) enable Cisco IOS network devices to announce themselves to their neighbors. By default, Cisco devices send a CDP announcement out every interface once per minute. If they receive a CDP announcement, they store that information in a table with a hold time of 3 minutes.
The potential problem with CDP and LLDP is that they provide an easy reconnaissance vector to any attacker with an Ethernet connection. When the switch sends a CDP or LLDP announcement out of a port where a workstation is connected, the workstation normally ignores it.
However, with a simple tool such as WireShark, an attacker can capture and analyze the CDP or LLDP announcement. Included in the CDP or LLDP data is the model number and operating system version of the switch. An attacker can then use this information to look up published vulnerabilities that are associated with that operating system version and potentially follow up with an exploit of the vulnerability.
Disable these protocols globally with the no cdp run/no lldp run commands, or disable them on a per-interface basis with the no cdp enable/no lldp enable commands.