Follow me on Twitter: https://twitter.com/CCNADailyTIPS
My strategy to pass CCNA Security in 6 MONTHS: https://www.youtube.com/watch?v=TRqDG…
Video 1: https://www.youtube.com/watch?v=loUUW…
Video 2: https://www.youtube.com/watch?v=qv-mm…
Video 3: https://www.youtube.com/watch?v=LKhP2…
Video 4: https://youtu.be/NK7uaqr2fgM
Video 5: https://youtu.be/FBCfrWImz2E
1.1 Common security principles
Confidentiality: Only authorized person can view. Integrity: The data hasn’t been modified by an unauthorized users. Availability: The data is available to authorized users when and where they need it.
SIEM: It is a live log and event management of a network
1.1.c Identify common security terms
Asset – Property, people, information/data (This is what we want to protect with CIA) Vulnerability – Weakness in a system or design (Maybe a firewall is unpatched) Threat – Potential danger to Assets. Risk – Potential for unauthorized access to compromise, destroy, or cause damage (Firewall with no PW, Reset our network devices, no network access). Countermeasure – Mitigates potential RISK. (a Firewall, blocking port and access) .
1.1.d Identify common network security zones
Private: The private, trusted network is commonly referred to as the “inside” security zone (controlled by us) Public : The public, untrusted network is commonly referred to as the “outside” security zone (cannot control) DMZ: This zone usually contains a relatively small number of systems whose services are made available to systems residing in the outside zone.
1.2 Common security threats
1.2.a Identify common network attacks
- Reconnaissance
- Social Engineering
- Backdoor
- brute force
- Privilege escalation
- botnets DDoS
- Man-in-the-middle
How to protect against attacks
- Least Privilege
- Role rotation
- Auditing
- Defense in depth
Describe social engineering
- Phishing
- Phone Scams
- Malverstin
Identify malware
- NetFlow
- IPEvents
- Snort
1.2.d Classify the vectors of data loss/exfiltration
- IP
- Credit cards
- PII
1.3 Cryptography concepts
Hash Algorithm – a fixed value used data for integrity. Symmetric – Same key to encrypt and decrypt. Faster, use less CPU, and used to encrypt VPN traffic to encrypt HTTPS. Asymmetric – Private and Public key used to encrypt and decrypt. Slower, use more CPU, and used to encrypt VPN authentication and it is used to send over the symmetric shared public key.
Digital signatures – A signature used to sign data. Certificates – issue by the CA used to identify, our asymmetric public and private key. PKI – is the infrastructure manage keys and certificates.
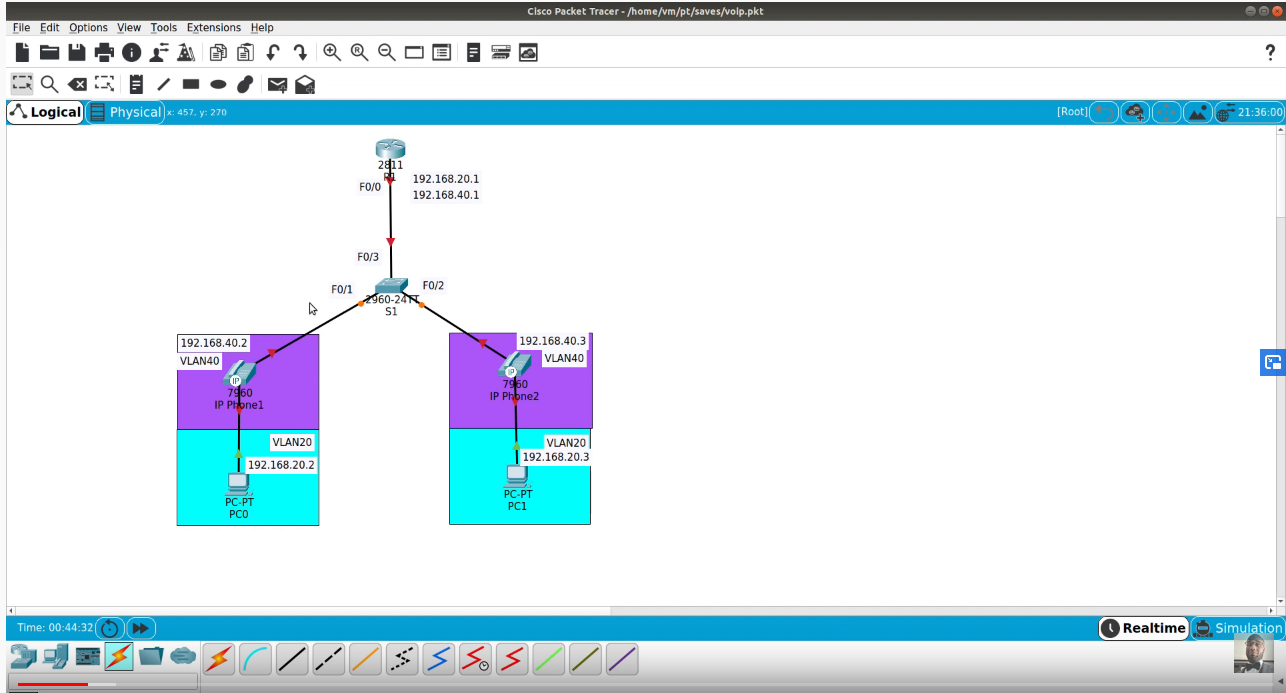
1.4 Describe network topologies
CAN – Multiple LANs connected in a limited area. WAN – Multiple LANs connected in a large geographic area. Data Center – a facility that host large servers. SaaS – Host software and license applications (OneDrive). PaaS – Provides you with software and hardware power. IaaS – provides you with everything you need over the internet: firewall, storage, and OS.