Get 30% off ITprotv.com with PROMO CODE CCNADT Follow me on
Twitter: https://twitter.com/CCNADailyTIPS
Take the Quizlet: https://quizlet.com/_6qbfal
ITProTV Lab:
My strategy to pass CCNA Security in 6 MONTHS:
https://www.youtube.com/watch?v=TRqDG…
Video 1: https://www.youtube.com/watch?v=loUUW…
Video 2: https://www.youtube.com/watch?v=qv-mm…
Video 3: https://www.youtube.com/watch?v=LKhP2…
Video 4: https://youtu.be/NK7uaqr2fgM
Video 5: https://youtu.be/FBCfrWImz2E
Video 6: https://youtu.be/kb7lgscxt4A
Video 7: https://youtu.be/av381O7mEVA
Video 8: https://youtu.be/vKaFfvc1Xm0
Video 9: https://youtu.be/8fPE7JdI-yk
Video 10 : https://youtu.be/uPiIC54SQlM
Video 11: https://youtu.be/4XXz4vg25gw
Video 12: https://youtu.be/TRwyMv_u_U4
Video 13: https://youtu.be/–oBDwISIPA
Video 14: https://youtu.be/KWwV-ULqMeI
Video 16: https://youtu.be/PwPfolXx5uI
2.3.a Identify the functions 802.1X components
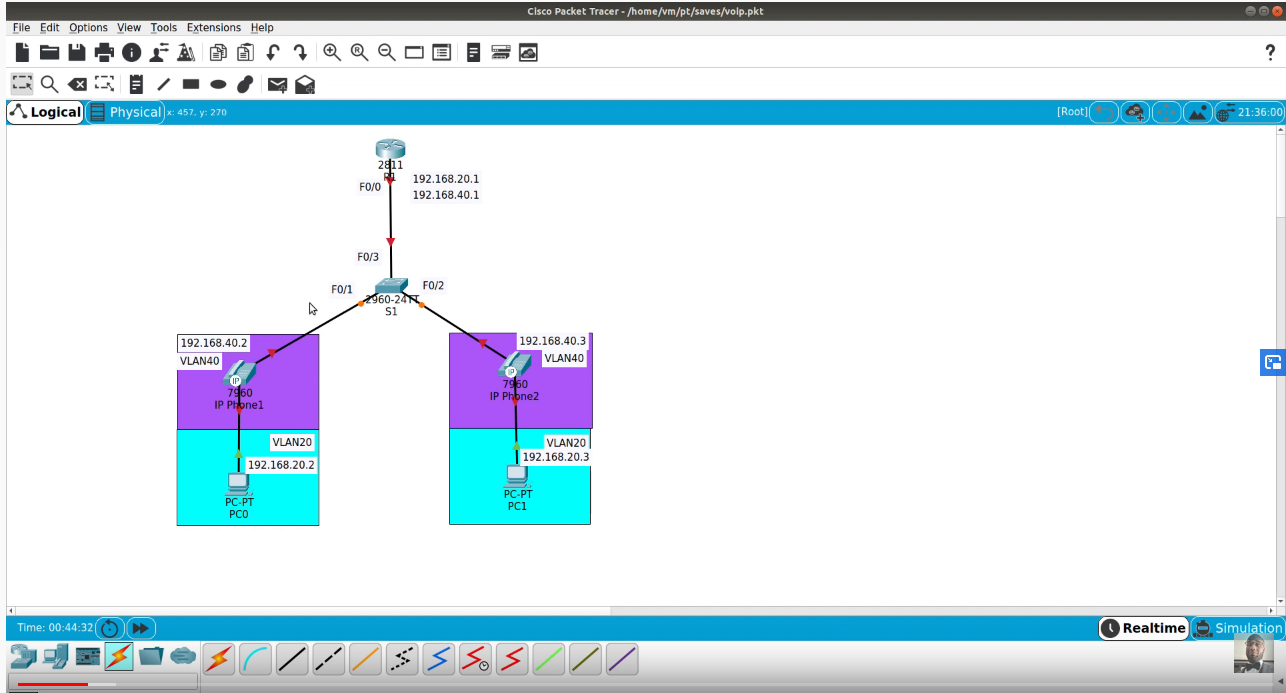
IEEE 802.1X is an IEEE Standard for port-based Network Access Control (PNAC). It is part of the IEEE 802.1 group of networking protocols Port based authentication provides a security mechanism to allow or disallow connectivity to a device connected to a specific port. The device attempting to connect to such a port is called a supplicant. The supplicant can be an end user device, such as a computer or an IP telephone, or it can be another network device.
Overview
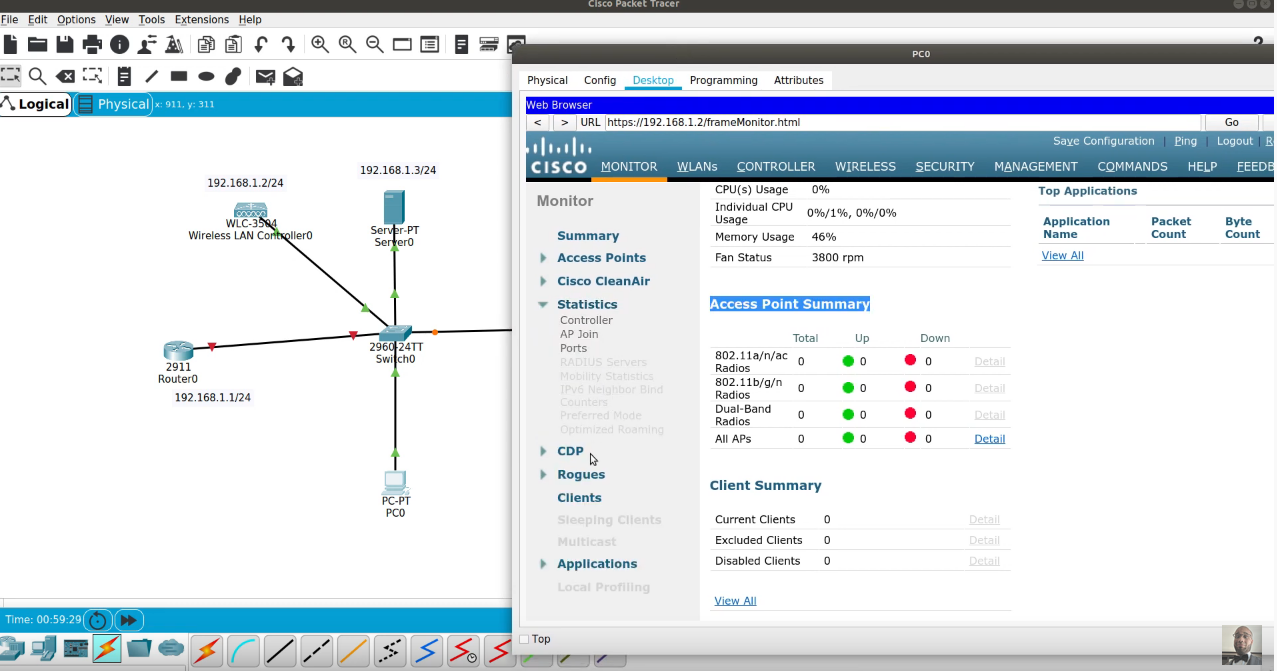
802.1X authentication involves three parties: a supplicant, an authenticator, and an authentication server. The supplicant is a client device (such as a laptop) that wishes to attach to the LAN/WLAN. The term ‘supplicant’ is also used interchangeably to refer to the software running on the client that provides credentials to the authenticator. The authenticator is a network device which provides a data link between the client and the network and can allow or block network traffic between the two, such as an Ethernet switch or wireless access point; and the authentication server is typically a trusted server that can receive and respond to requests for network access, and can tell the authenticator if the connection is to be allowed, and various settings that should apply to that client’s connection or setting. Authentication servers typically run software supporting the RADIUS and EAP protocols. In some cases, the authentication server software may be running on the authenticator hardware.
Overview
The authenticator acts like a security guard to a protected network. The supplicant (i.e., client device) is not allowed access through the authenticator to the protected side of the network until the supplicant’s identity has been validated and authorized. With 802.1X port-based authentication, the supplicant must initially provide the required credentials to the authenticator – these will have been specified in advance by the network administrator, and could include a user name/password or a permitted digital certificate. The authenticator forwards these credentials to the authentication server to decide whether access is to be granted. If the authentication server determines the credentials are valid, it informs the authenticator, which in turn allows the supplicant (client device) to access resources located on the protected side of the network.